🦞 The "Lobster" OS: NVIDIA's NemoClaw and the Age of Agentic Computing
GM tech enthusiasts! 🤖 We've moved beyond "AI that thinks" to "AI that acts." NVIDIA's NemoClaw isn't another chatbot. It's the operating system for AI agents—autonomous software that books flights, manages emails, writes code, and executes workflows. The shift: From software as tool → software as active participant. Today's breakdown: 🦞 The "Lobster" model (hard shell security, soft core intelligence) 🔒 Privacy Router (local vs. cloud routing) 🧠 Nemotron 3 portfolio (specialized AI models) 💼 "Salary + Tokens" economy (AaaS replaces SaaS) 🚀 OpenClaw's viral growth (80k GitHub stars in weeks) Let's dive in! 🚀 🦞 The "Lobster" Model: Hard Shell, Soft Core NVIDIA's central metaphor: Agents need two components: Soft core = Intelligent LLM (reasoning) Hard shell = NVIDIA OpenShell (security) NVIDIA OpenShell: Isolates each agent session into process-level container Windows: Powered by WSL (Windows Subsystem for Linux) "Out-of-process" security = infrastructure-enforced safety Why this matters: Old approach: Hope model "behaves" (alignment) New approach: Enforce safety at infrastructure level Even if agent is hijacked via prompt injection, the hard shell prevents: ❌ Sandbox escape ❌ Host system access ❌ Unauthorized actions Browser tab model for AI. Each agent = isolated process. 🛡️ 🔒 The Privacy Router: Ending "Cloud vs. Local" The enterprise dilemma: Cloud = powerful reasoning, bad for sensitive data Local = secure, but weaker models NemoClaw's Privacy Router solves this: Three routing paths: 1. Local Execution Proprietary code, PII, trade secrets Stays on RTX PC or DGX Spark Never touches cloud 2. Cloud Routing Non-sensitive tasks needing frontier reasoning Sent to cloud models (GPT-5, Claude Opus, etc.) 3. Sanitized Cloud Routing Hybrid tasks stripped of identifiers Reasoning happens in cloud Context re-injected locally Example: "Analyze this customer contract and suggest pricing." Sanitized route: Removes: Customer name, company, specific terms

🏦 Interest Rate Arb & Delta-Neutral Strategies: The 2026 Playbook
https://interest-arb.web.app/#foundation The DeFi lending landscape just hit a new level of sophistication — and there are real edges hiding in the spread between protocols right now. Let's break it all down. 📊 The Lay of the Land The stablecoin market cap just crossed $310 billion. DeFi lending isn't experimental anymore — it's financial infrastructure. The most important number to know: the Sky Savings Rate (sUSDS) = 3.75% APY. This is the de facto yield floor for stablecoins, backed by $1.5B+ in real-world assets. Any protocol charging you significantly more to borrow than 3.75% is pricing in risk — or it's an arb opportunity. Translation: if you can borrow below 3.75% or earn above it, you have a trade. The big three lending protocols right now: 🔵 Aave v3 — $44B+ TVL, 60% of the decentralized borrowing market, just launched V4 "Frontier" 🟣 Morpho Blue — $13B+ TVL, modular architecture, 70% lower gas than legacy protocols 🟡 Euler v2 — permissionless vault architecture, 85%+ capital utilization Plus Pendle for yield tokenization and Contango as the 1-click execution layer for all of this. ⚙️ The Core Mechanic: Recursive Lending (Looping) This is the engine behind almost every strategy we'll talk about. The formula: L = 1 / (1 − LTV) 90% LTV (Aave E-Mode stablecoins) = up to 10× leverage 82.5% LTV (ETH/USDC) = up to 5.7× leverage 93% LTV (stablecoin pairs) = up to 14.3× leverage The loop: deposit yield-bearing collateral → borrow a lower-cost stablecoin → swap for more collateral → re-deposit → repeat. Key insight: On Aave, your collateral earns supply interest while it sits there. On Morpho, collateral is typically idle unless you're peer-to-peer matched. That makes looping structurally more profitable on Aave for certain pairs. 🎯 The Four Core Strategies 1. Delta-Neutral Stablecoin Looping (Aave, Arbitrum) Supply $10K USDC → enable E-Mode → borrow USDT → swap to USDS → re-deposit → repeat ~4 times
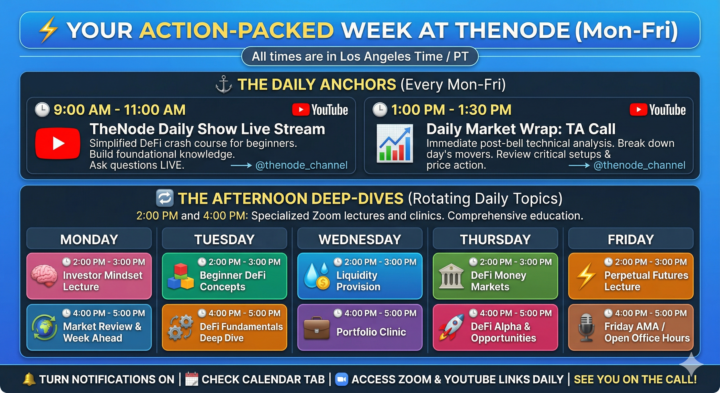
🗓️ Our New Weekly Master Schedule: Mark Your Calendars! 🚀
Hey everyone! We’ve got an action-packed week ahead. To make sure you never miss a beat, I want to break down our new daily schedule. We have four scheduled calls every single weekday. The 9:00 AM and 1:00 PM calls are our daily staples, while the 2:00 PM and 4:00 PM sessions rotate topics throughout the week so we can cover everything from mindset to advanced DeFi strategies. (Note: All times are in Los Angeles Time / PT) ⚓ The Daily Anchors (Every Mon-Fri) 🕘 9:00 AM - 11:00 AM | TheNode Daily Show Live Stream - Where: YouTube: https://www.youtube.com/@thenode_channel - What: New to crypto? 🚀 This is your daily crash course in the basics! We simplify DeFi to prepare you for the big leagues. Join live, ask questions, and build the foundational knowledge you need to succeed. 🕐 1:00 PM - 1:30 PM | Daily Market Wrap: TA Call - Where: YouTube: https://www.youtube.com/@thenode_channel - What: Immediately after the bell, we break down the day’s biggest movers with deep technical analysis. Don't trade blindly—review the session's most critical setups and price action with us! 🔄 The Afternoon Deep-Dives (Rotating Daily Topics at the same time each day) At 2:00 PM and 4:00 PM, we jump into Zoom for specialized lectures and clinics. The topics change daily so we can give you a comprehensive education. The times for these daily calls are the same each day. Here is what Monday looks like: - 🕑 2:00 PM - 3:00 PM | Investor Mindset Lecture: Master the psychology of successful investing. We'll work on detecting cognitive biases, building discipline, and developing emotional resilience. Your mindset is your edge! - 🕓 4:00 PM - 5:00 PM | Market Review & Week Ahead: Start your week with a comprehensive market analysis. We break down the previous week's price action, identify key trends, and map out opportunities and risks. A Sneak Peek at the Rest of the Week's Afternoon Sessions:
🎯 Advanced Delta Mechanics: Risk, Hedging, and Statistical Edge
Hello All! This briefing synthesizes advanced quantitative frameworks for understanding Delta beyond its basic interpretation as a share-equivalent exposure. Institutional risk management requires a departure from retail-level heuristics, focusing instead on the mathematical divergence between Delta and true probability, the impact of second-order Greeks (Vanna and Charm), and the structural mechanics of 0DTE options. 🔑 Critical Takeaways 📐 Delta vs. Probability Delta (N(d₁)) is a dynamic hedge ratio, not a static probability of expiring In-The-Money. It systematically overstates the true risk-neutral probability (N(d₂)) — particularly as volatility or time to expiration increases. 🌊 Second-Order Drivers Market directionality is often driven by "hidden" layers of exposure — Vanna (sensitivity to volatility changes) and Charm (Delta decay over time) — which dictate institutional hedging flows like the "Charm bid." 💥 The Expiration Singularity The proliferation of 0DTE options has concentrated Gamma and Delta risk into high-velocity intraday windows, creating "Pin Risk" where underlying prices are magnetically tethered to heavy open-interest strikes. ⚙️ Hedging Efficiency Continuous dynamic Delta-hedging is often mathematically suboptimal due to transaction friction and overnight price jumps. Static hedging architectures and threshold-based models utilizing a Minimum Variance Delta provide superior risk-adjusted returns. 📊 Portfolio Standardization Managing multi-asset risk requires Beta-Weighting to normalize disparate positions into a single SPY-equivalent metric — accounting for the "Overnight Effect" where Charm and Vanna cause significant structural Delta drift while markets are closed. 1. 📐 The Mathematical Foundations of Delta In institutional quantitative frameworks, Delta is defined under the Black-Scholes-Merton (BSM) model as a functional proxy rather than a linear assumption. Delta as a Hedge Ratio (N(d₁)) While often mischaracterized as the probability of an option expiring ITM, Delta is strictly a risk-adjusted hedge ratio. Under BSM, the price of a European call option is:
6
0

🔍 Intelligence Brief: Constellation Network ($DAG) & the "America's Blockchain" Thesis
One of the more interesting figures in the non-DeFi crypto space right now is Patrick Flood — aka Dagnum P.I. — and his work deserves a serious look, even if you're primarily a DeFi person. Here's why. 🪖 Who Is This Guy? Patrick Flood is not your typical crypto influencer. His background: U.S. Army Special Operations Command (USASOC), deployed to Iraq and Afghanistan Trained in intelligence operations and the OODA loop (Observe, Orient, Decide, Act) Professional actor in LA (explains the high production quality) Founded "Owners in Honor" — a consultancy helping veterans with business brokerage and valuation He now runs the Stardust Collective, a community initiative within the Constellation ecosystem, and operates directly between the core executive team and the public. His role is essentially: translate complex DoD-level tech developments into digestible intelligence for the community. The "P.I." branding isn't accidental — he frames his output as vetted intelligence, not hype. 💡 The Core Thesis: A Cybersecurity Tipping Point Flood's central argument: Web2 security is fundamentally broken because of centralized data silos. Every major breach, identity theft event, and data tampering incident makes the case stronger. His prediction: the U.S. government will eventually mandate Distributed Ledger Technology for mission-critical data validation — and Constellation's Hypergraph Transfer Protocol (HGTP) will be the infrastructure it runs on. This isn't retail crypto speculation. It's a DoD procurement narrative. The aviation example makes it concrete: A single aircraft generates 25 million ACARS events every 24 hours. That's sensor data, communications, navigation logs — all of it vulnerable to spoofing and injection attacks. HGTP validates data at the edge (at the source) rather than after it's already been transmitted and potentially tampered with. The U.S. Air Force is the use case he keeps coming back to. 🏛️ Iron SPIDR: The Federal Integration Program
0
0

1-30 of 301

skool.com/defiuniversity
Master DeFi from beginner to advanced. Security-first curriculum, live mentorship, gamified learning. Join us and build DeFi expertise safely.
Powered by




