Activity
Mon
Wed
Fri
Sun
Jun
Jul
Aug
Sep
Oct
Nov
Dec
Jan
Feb
Mar
Apr
What is this?
Less
More
Memberships
AI Automation Station
2.6k members • $9/month
AI Automation First Client
1.6k members • Free
AI Automation Agency Hub
314k members • Free
AI Automation Society
349.4k members • Free
57 contributions to AI Automation Society
I sold my AI agency. here's the playbook
In September 2024 I started an AI automation agency. Nine months later I was doing $100K/month in recurring revenue. Then I sold my share to my partners. I took everything I learned: - The client acquisition system - The pricing - The delivery process … and I turned it into a step-by-step playbook for building a one-person AI agency. No code. No team. No guesswork. See exactly what's inside: -> I sold my AI agency. here's the playbook PS: If you are an AIS+ member, this is included in the Scale module. No need to purchase separately. - Nate
Looking for Sales Closers in the USA & Canada (High-Value Services)
We’re actively looking for experienced professionals who can identify leads, engage decision-makers, and close deals in the US & Canada markets. We offer high-demand, easy-to-sell services across AI, digital growth, and cybersecurity: - AI Audit Services - Website Development, SEO & AEO Optimization - Social Media Content Factory - Virtual CISO (CISO-as-a-Service) 💰 What’s in it for you: - Attractive payouts / commissions - High-ticket services with recurring revenue potential - Full backend delivery handled by our team - Long-term earning opportunity 👉 If you have the ability to open doors and close deals, we’re ready to work with you. DM me or reach out directly to get started.
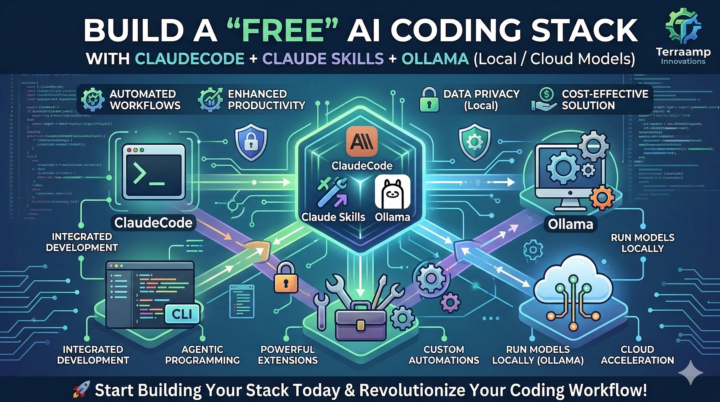
Build a “Free” AI Coding Stack with ClaudeCode + Claude Skills + Ollama (Local / Cloud Models)
Why this combo is interesting If you want an AI-assisted coding workflow without paying for hosted inference, you can combine: - ClaudeCode as your coding workflow (prompts, refactors, tests, review loops) - Claude Skills (Skill Creator) as your reusable automation layer (repeatable “mini-agents” like “Write PR description”, “Generate unit tests”, “Create API client”, etc.) - Ollama as your free local model runtime (run models on your laptop/workstation) The result: a practical “local-first” setup where your day-to-day coding helpers run on Ollama at $0 inference cost (hardware permitting) / Cloud model with rate limiting, while you still get a structured workflow via ClaudeCode + Skills. What you can build with this stack Full & Detailed Article is here. https://www.linkedin.com/pulse/build-free-ai-coding-stack-claudecode-claude-skills-local-dogiparthy-btohc/?trackingId=OV8Oh%2FTzwGYCazobvxJ%2BaQ%3D%3D
🚀New Video: Claude Code Skills Just Got Even Better
2 videos in one day?? Had to do it... Claude Code just dropped a major update to how skills work. The new Skill Creator helps you build better skills from scratch, run evals to test how they perform, optimize existing skills for better accuracy, and trigger them more reliably. In this video, I break down everything that changed and then do a full live build of a brand new skill so you can see exactly how it works. Whether you're just getting started with Claude Code or you've already been building skills, this update makes the whole workflow significantly better.
From Cost Center to Strategic Advantage: The Rise of the vCISO
Cyber risk is no longer just an IT problem - it is a boardroom priority. Yet many mid-sized and growing organizations face a difficult reality: - Threats are increasing - Compliance requirements are expanding - Customers are demanding security assurance But hiring a full-time CISO is expensive and often unjustifiable In India and globally, a seasoned Chief Information Security Officer can cost ₹1.2 Cr – ₹3 Cr annually when you factor in salary, benefits, tooling, and support structure. For many organizations, that investment simply does not align with their current scale. This is exactly where the Virtual CISO (vCISO) model is transforming the market. 🔍 What a Modern vCISO Actually Delivers A mature vCISO is not just an advisor who shows up for quarterly reviews. Done right, it provides continuous, structured cyber governance: ✅ Continuous risk visibility ✅ Compliance posture tracking ✅ Incident readiness ✅ Vendor risk oversight ✅ Executive-level reporting ✅ Security roadmap aligned to business growth The key shift is moving from periodic consulting to continuous security leadership as a service. 💰 The Cost Advantage Is Significant Let’s look at a typical comparison: - Full-Time CISO ₹1.2 Cr – ₹3 Cr per year - Additional team costs - Tooling overhead - Limited scalability AI-Enabled vCISO (Modern Model) - Fraction of the cost - Scales with business size - Continuous monitoring - Automated evidence collection - Faster audit readiness For many mid-market firms, this translates to 60–70% cost optimization while improving security maturity. 🧠 The TerraAmp Perspective At TerraAmp Innovations, we believe the next evolution of cyber leadership must be: - Continuous - Intelligence-driven - Context-aware - Automation-assisted - Business-aligned Our vCISO platform is designed to give organizations enterprise-grade security governance without enterprise-grade overhead. Because in today’s threat landscape, the real question is no longer: “Can we afford a CISO?”
1
0

1-10 of 57
@sree-dogiparthy-4142
Helping Companies Evolve Beyond Automation | Multi-Agent Cloud & DevOps Architect | Generative AI | 20+ Yrs in IT | 10+Yrs in Cloud & DevOps
Active 15h ago
Joined Dec 2, 2025
Powered by


