
Write something
⚓️ €5 tracker, €500M warship, zero surprises for anyone doing OSINT.
Last week, Dutch broadcaster Omroep Gelderland tracked the location of Zr. Ms. Evertsen, a Dutch air-defense frigate escorting France’s Charles de Gaulle carrier in the eastern Mediterranean, by mailing a generic Bluetooth tracker (basically a cheap AirTag clone, the kind you buy on AliExpress for five euros) inside a greeting card via military postal service. The tracker piggybacked on Apple’s Find My network, relaying its position through any nearby iPhone. From the sorting center in the Netherlands to Crete to 24 hours at sea, the frigate’s route was mapped in real time. The security establishment panicked. Defensie banned greeting cards containing batteries from being sent to the ship. The minister briefed parliament. But this isn’t news. It’s confirmation.The Evertsen was trackable from the moment it left Den Helder. You could find that ship without the tracker. Most military vessels operating outside active conflict zones are already fully exposed through public infrastructure: AIS broadcasts (MarineTraffic, VesselFinder), crew social media leakage (Strava, LinkedIn), port webcams, satellite imagery, and vessel registries. The Bluetooth story got traction because it’s visceral. A postcard, five euros, a journalist. It feels like a breach because it is one. But it’s a symptom. The disease is operational security built on the assumption that a modern warship can hide in the most observed maritime zone on the planet. It can’t. For compliance and intel professionals: this is a live case study in exposure collapse. The infrastructure
🥂 Thank You: ONE HUNDRED MEMBERS
We just hit 100 members. I’m building this on my own, so reaching this milestone genuinely means a lot to me. Thank you to everyone who joined, followed along, asked questions, and supported what I’m building here. More courses are coming soon. I’m actively working on new material and expanding the platform step by step. Before I decide what to build next, I want to ask you: 👉 What would you like to see next? Topics, formats, depth, anything goes. Drop your thoughts below. This community helps shape what comes next Appreciate every one of you. The best is yet to come. Cultro Distro

🔫 The Ideal Concealed Carry: A Minnesota Original
Back in 2016, someone in Minnesota really said: what if a gun looked like a smartphone. Developed by Kirk Kjellberg, this folding pistol was sold under AutoLaunce, formerly available via Ideal Conceal. When closed, it looks like a regular phone. Flip it open, and it becomes a two-barrel .380 ACP handgun. It dropped in the middle of peak smartphone culture and instantly caused chaos, some people called it genius concealment, others called it reckless as hell. Production eventually stopped, but the 2016 “phone gun” is still one of the wildest concealment designs ever put on the market.

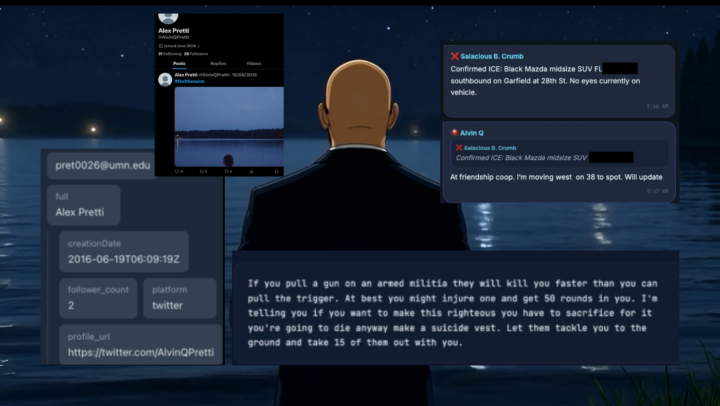
🧊 Socials 101 — OSINT Case Preview: What can you expect?
Ahead of the upcoming Socials 101 course, here’s a real-world example showing how open-source social analysis works when timing, aliases, and behaviour intersect. In the upcoming course I will be teaching you how to this and more, professionally. 📲 In a Signal group chat linked to a protester network in Minneapolis, analysts observed that at 8:47 CST, a user named “Alvin Q” replied to another participant (Salacious B. Crumb) stating that he “will update” on the location of a suspected ICE vehicle. The vehicle was described as being approximately 8 blocks from where a shooting was reported about 15 minutes later. That message became a pivot point. 🔎 Using only open-source techniques, the handle “Alvin Q” was correlated to the alias AlvinQPretti. That alias appears in breach-derived username data linked to the email address [email protected], to a dormant X (Twitter) account created in 2016. 📍 The Signal user also displayed a medic emoji, which aligns with publicly reported biographical information about Alex Jeffrey Pretti. - Graduate of the University of Minnesota (2011), degree in biology, society and the environment - Employed as an ICU nurse - Worked for the U.S. Department of Veterans Affairs at the Minneapolis VA Health Care System 📉 After the reported shooting window, Alvin Q did not send any further messages in the Signal group. What this OSINT pattern demonstrates • Alias and username reuse across platforms • Timestamp correlation between chat activity and real-world events • Behavioral analysis (sudden silence as a data point)e • Emoji and profile indicators as contextual signals • The importance of what not to conclude No hacking. No private access. No assumptions beyond the data. This is exactly the type of structured social-media OSINT we’ll break down step-by-step in Socials 101: ✔ Mapping the social attack surface ✔ Alias & handle pivoting ✔ Timeline reconstruction ✔ Signal vs noise in live events ✔ Ethical limits and analytical restraint
🕵️♂️ Google is showing fewer results lately, this can affect your investigations
If you’ve noticed Google giving you fewer results than before, you’re not imagining things. This makes finding hidden info, old pages, or public documents harder, this is a big deal for OSINT work. ✅ The fix: search smarter. Use Google Dorking: advanced search tricks that make your results way more precise. Try: - site: → search within one website - filetype: → look for PDFs, DOCXs, or XLSXs - intitle: / inurl: → find words in titles or URLs - "quotes" → exact phrases 💡 Example: site:example.org filetype:pdf "annual report" ⚖️ Reminder: Only use these methods on public data or systems you’re authorized to test. Always keep your OSINT ethical and legal.
1-11 of 11
powered by

skool.com/huisvestnl-3698
Get started in OSINT and learn how to find out about anything and anyone online, professionally.
Suggested communities
Powered by
