Activity
Mon
Wed
Fri
Sun
Jun
Jul
Aug
Sep
Oct
Nov
Dec
Jan
Feb
Mar
Apr
May
What is this?
Less
More
Memberships
CyberMAYnia CAREER
419 members • Free
Smart Saver Society
1.5k members • Free
CyberMAYnia Club
61 members • Free
CISSP Study Group
2.1k members • Free
21 contributions to CISSP Study Group
CISSP Practice Question (Domain 2: Asset Security - AI Exam Guidance)
A marketing team wants to fine-tune a public LLM using five years of customer support transcripts to improve chatbot responses. The transcripts contain names, email addresses, and billing details. What should the security manager require BEFORE the fine-tuning begins? A. A signed NDA with the LLM vendor covering all training data B. Data masking or tokenization of PII within the transcripts C. Customer consent emails authorizing the use of their conversations D. A data processing agreement executed with the cloud provider Come back for the answer tomorrow, or study more now!
CISSP Practice Question (Domain 1: Security and Risk Management - AI Exam Guidance)
Your company's HR department deploys a resume-screening AI tool without consulting security or legal. A rejected applicant files a discrimination complaint claiming the tool filtered out candidates based on age. Who should the CISO escalate to FIRST? A. The AI vendor to request bias testing documentation B. Legal counsel to assess regulatory exposure from the unauthorized deployment C. The HR director to immediately disable the tool D. Internal audit to begin a full algorithmic fairness review Come back for the answer tomorrow, or study more now!
AI Exam Guidance - CISSP Practice Question (Domain 3: Security Architecture and Engineering)
A healthcare company deploys a diagnostic AI system that recommends treatment options. Regulators require the organization to explain how the model reaches its conclusions. The security architect proposes encrypting the model's internal weights to protect intellectual property. What concern should the CISO raise FIRST? A. Encryption at rest is insufficient without also encrypting data in transit between inference nodes B. Protecting model weights may conflict with the regulatory requirement for explainability C. The model should be hosted in a secure enclave to prevent adversarial extraction attacks D. A third-party penetration test should validate the encryption implementation before deployment Come back for the answer tomorrow, or study more now!
CISSP Practice Question – Software Development Security (AI-Assisted SDLC & Risk Governance)
A global fintech company adopts an AI-assisted code-generation platform to accelerate development.The CISO learns that developers sometimes allow the tool to access proprietary source repositories and external training data. Management wants faster delivery but is concerned about intellectual-property leakage and unvetted open-source dependencies being inserted into production builds. What is the BEST control to implement FIRST? A. Require legal review of the vendor’s AI license terms and intellectual-property indemnification clauses. B. Integrate automated software-composition analysis (SCA) and code-signing into the CI/CD pipeline to validate all generated components. C. Restrict the AI tool’s access to internal repositories and enforce output review through secure-coding peer validation. D. Mandate retraining of the AI model using only internal proprietary data to eliminate third-party influence.
CISSP Practice Question – Security Operations (BCP/DRP vs. Forensic Recovery)
A ransomware attack encrypts multiple servers, including systems that store financial transaction data. Management activates the disaster recovery plan to restore from clean backups and resume business operations as quickly as possible. Meanwhile, law enforcement and internal investigators request that the affected systems remain offline to preserve evidence for criminal prosecution. What is the BEST course of action? A. Prioritize rapid system recovery and resume operations immediately using backups to meet RTO objectives. B. Delay full recovery until investigators complete forensic imaging and evidence collection. C. Restore essential systems first, while creating verified forensic images of compromised hosts before reinitialization. D. Refuse to proceed with any restoration until the court issues a warrant authorizing evidence handling.
1-10 of 21
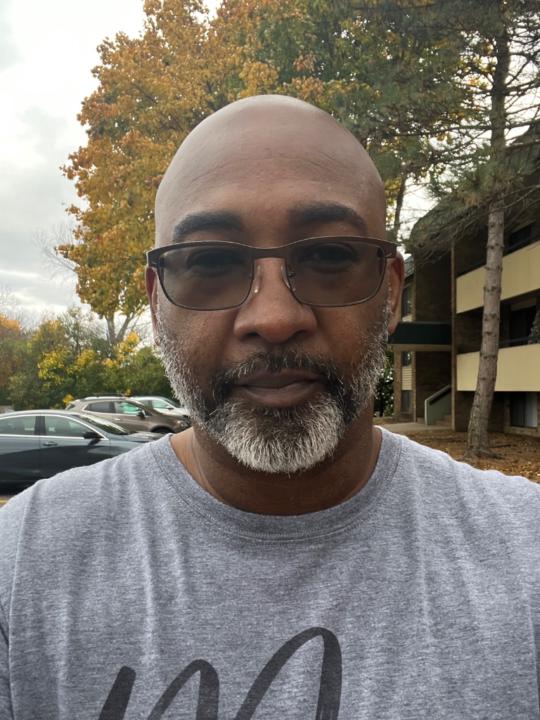
@ryan-battles-2313
Cyber Security Professional - AI Enthusiast | Asset Security | GRC | IoT / OT Security | Cloud & Network Security | Security Engineering | Mentor
Active 3h ago
Joined Jul 10, 2025
Powered by