
Write something
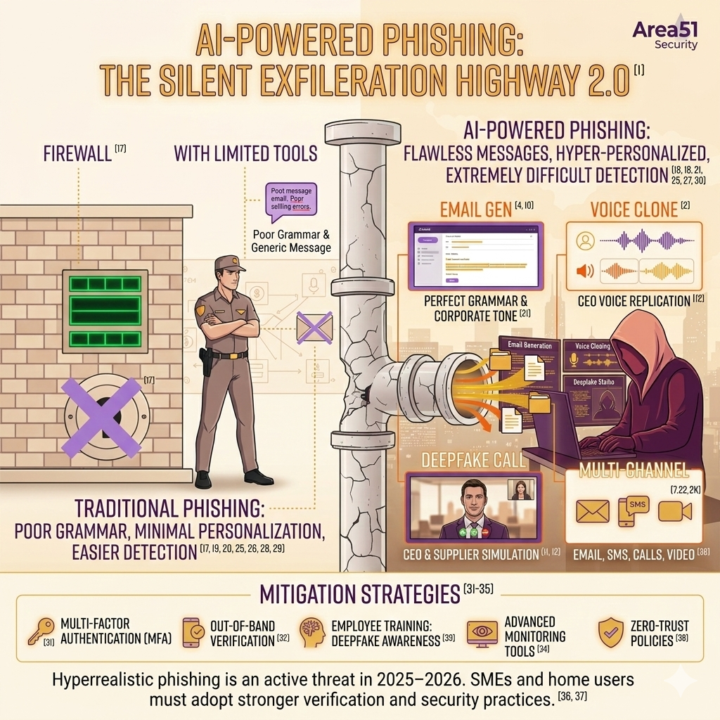
Hyperrealistic Phishing with Generative AI (2025–2026)
Executive Summary Phishing has transformed into a new generation of attacks powered by generative AI. Fraudsters now deploy flawless emails, cloned voices, and deepfake video calls to bypass traditional defenses. This evolution poses severe risks for small and medium-sized enterprises (SMEs) and home networks, where verification processes are often minimal. How It Works - Generative AI models produce corporate-style emails and chat messages indistinguishable from legitimate communication. - Voice cloning replicates executives’ voices using publicly available recordings. - Deepfake video calls simulate real-time meetings with avatars of CEOs or suppliers. - Multi-channel campaigns combine email, SMS, and calls to reinforce credibility. Documented Cases (2025–2026) - Kaspersky Q2 2025 Report: Recorded a 41% increase in phishing attempts in Europe, blocking over 142 million malicious clicks in a single quarter. Many campaigns used AI-generated content and voice cloning. - Trend Micro 2025 Analysis: Identified spear-phishing campaigns infiltrating ongoing email threads, generating context-aware replies with AI. - Europol Cybercrime Centre (2025): Issued warnings about deepfake-enabled Business Email Compromise (BEC), where fraudsters impersonated executives in video calls to authorize wire transfers. Impact on SMEs and Home Networks - Financial losses: Fraudulent transfers ordered via cloned voices of CEOs. - Credential theft: Employees tricked into revealing login details. - Operational disruption: Malware delivered through convincing attachments. - Reputation damage: Customers and partners deceived by fake communications. Recommendations 1. Multi-factor authentication (MFA): Prevents stolen credentials from granting access. 2. Out-of-band verification: Confirm financial requests via independent channels. 3. Employee training: Awareness of deepfake calls and AI-generated fraud. 4. Advanced monitoring tools: Detect anomalies in communication patterns. 5. Zero-trust policies: Limit access privileges to reduce attack surfaces.
1
0
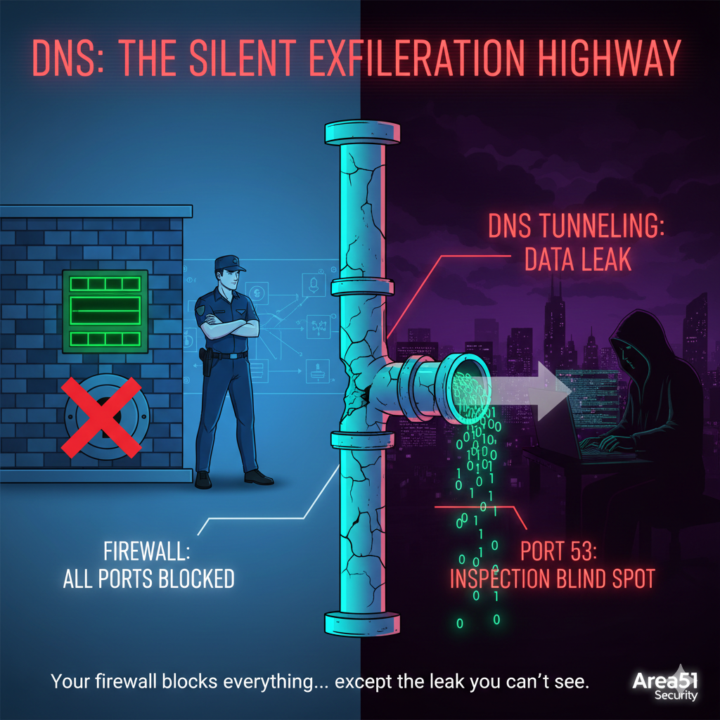
DNS: The Silent Exfiltration Highway
The Hook: Your firewall is blocking everything... except the one port that's leaking your data. - The Core: Most companies leave Port 53 (DNS) wide open. Attackers use "DNS Tunneling" to sneak data out of your network, one small query at a time. It looks like normal web traffic. - The Insight: If you aren't inspecting DNS traffic, you're flying blind. - The Question: Do you know which domains your servers are talking to right now? - - ----🍿 developing solutions, and earlier partnership inside the Area51 group.” -
1
0
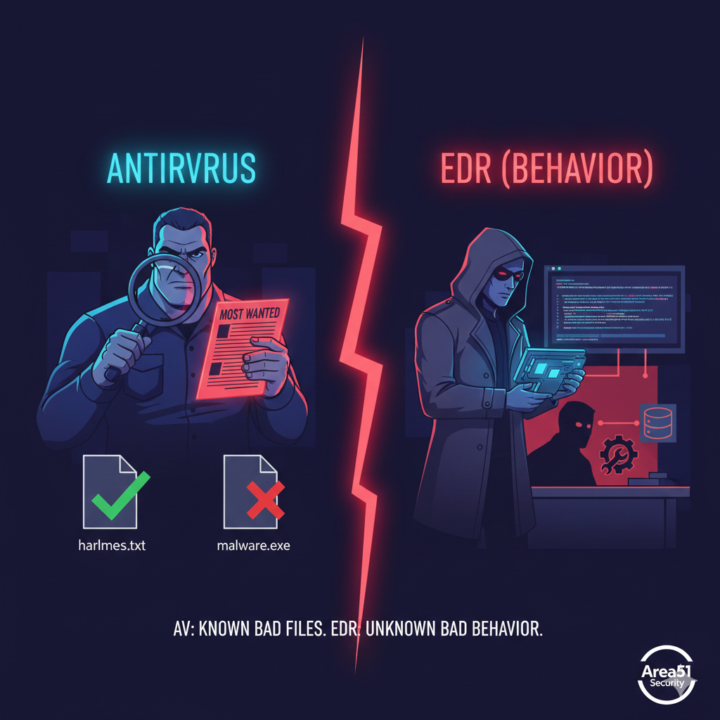
The "EDR vs. AV" Reality Check
The Hook: An Antivirus is a security guard with a "Most Wanted" list. An EDR is a private investigator. - The Core: If an attacker uses PowerShell to encrypt your drive, the AV sees a "trusted Windows tool" doing its job. The EDR sees a suspicious pattern of behavior. - The Insight: Prevention is ideal, but detection is mandatory. - The Question: If a legitimate admin tool started behaving like a wiper, would your system even blink? - - ----🍿 developing solutions, and earlier partnership inside the Area51 group.”
1
0
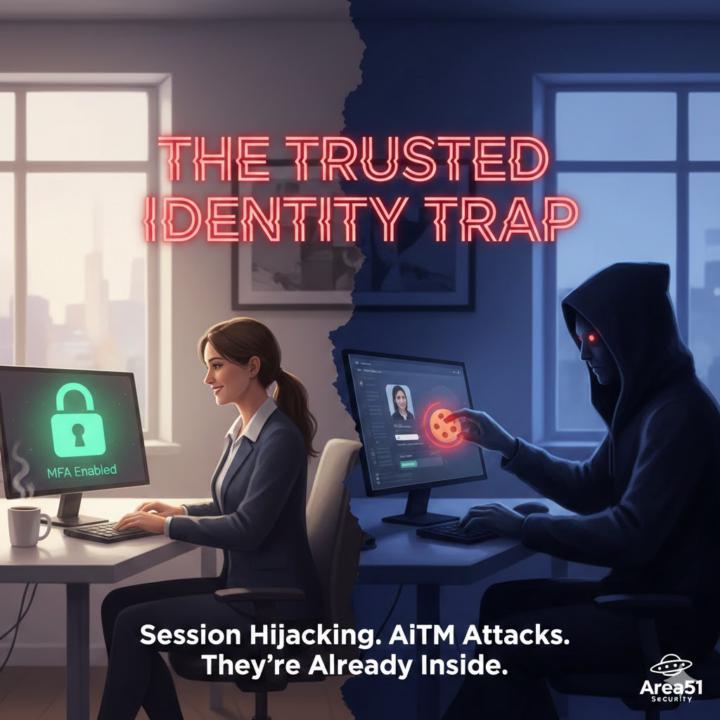
The "Trusted Identity" Trap
The Hook: Your biggest threat isn't a hacker. It's your most trusted employee's login at 3:00 AM. - The Core: MFA is no longer a "silver bullet." Session hijacking and Adversary-in-the-Middle (AiTM) attacks can bypass traditional MFA by stealing browser cookies. - The Insight: Attackers don't "break in" anymore; they "log in." - The Question: Are you monitoring where logins come from, or just assuming the password + code is enough? - ----🍿 We’re diving deeper into this inside the Area51 group.
1
0
Ransomware Is Going “Fileless” — And That’s a Big Problem
Most people think ransomware means “malicious files”.That’s no longer true. Today, many ransomware attacks use built-in system tools that already exist on your computer. No strange files. No obvious malware. What attackers are doing: - Using normal admin tools instead of custom malware - Running commands directly in memory - Moving across the network using legitimate remote access features Why this matters:Traditional antivirus looks for bad files.If there are no bad files… detection becomes much harder. Question for the group:Are your security tools focused on behavior, or mostly on known malware? ----🍿 We’re diving deeper into this inside the Area51 group.
1-8 of 8

