Activity
Mon
Wed
Fri
Sun
May
Jun
Jul
Aug
Sep
Oct
Nov
Dec
Jan
Feb
Mar
Apr
What is this?
Less
More
Owned by Digital
Start your cybersecurity journey, learn core skills, prepare for certifications, and build a path into the industry. Get the roadmap you need.
Memberships
Cybersecurity BootCamp
77 members • $2/month
CyberCircle
85.4k members • Free
Business Builders Club
7.8k members • Free
20 contributions to BREAKING INTO CYBERSECURITY
Top Cybersecurity Platforms for Beginners!
Top Cybersecurity Platforms for Beginners! If you want to start a career in cybersecurity and boost your skills, these are the best places to learn hands-on: TryHackMe | Hack The Box | PortSwigger | HackThisSite | Cybrary | Try2Hack | picoCTF | Root Me | UltraEdit Start your journey today and level up your cybersecurity career!
0
0

Companies Use These Cybersecurity Tools… And Still Get Hacked
90% of Companies Use These Cybersecurity Tools… And Still Get Hacked Cybersecurity isn’t about tools. But the wrong tools will expose you faster than any hacker. Most companies think they’re “secure” because they installed a few solutions. They’re just collecting tools… not building defense. Here’s what a real cybersecurity stack actually looks like 👇 🔹 Networking & Monitoring Wireshark | Nmap | Snort | SolarWinds → See what’s happening before it becomes a breach 🔹 Application Security Burp Suite | OWASP ZAP | Checkmarx | Veracode → Find vulnerabilities before attackers do 🔹 Cloud Security Prisma Cloud | AWS Security Hub | Microsoft Defender | Lacework → Because your data isn’t on-prem anymore 🔹 Incident Response & Intelligence TheHive | SANS SIFT | MISP | Xplico → Detect, respond, and learn from attacks 🔹 Password Cracking (Offensive Testing) John the Ripper | Hashcat | Hydra | Cain & Abel → If your passwords can’t survive this, they won’t survive attackers 🔹 Wireless Security Aircrack-ng | Kismet | WiFi Pineapple → Your WiFi is often your weakest entry point 🔹 Digital Forensics Autopsy | EnCase | FTK → Understand what really happened after the breach 🔹 Penetration Testing Metasploit | Kali Linux | Cobalt Strike | Burp Suite → Simulate real attacks before they happen Tools don’t make you secure. Blind confidence does the opposite. You can have the best stack in the world… and still get breached because no one knows how to connect the dots. Cybersecurity maturity = Tools + Strategy + People Miss one → You’re exposed. If you had to choose only 3 tools from this list to protect a company…
0
0

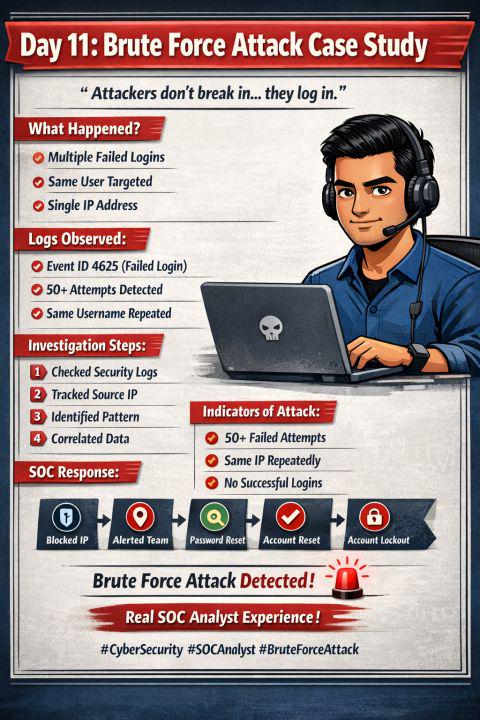
Brute Force Attack Case Study
💡 Reality Check: 👉 “Attackers don’t break in… they log in.” Today I worked on a real-world scenario 👇 💻 Case Study: Brute Force Attack Detection 🔍 What happened? 📌 Multiple failed login attempts 📌 Same user account targeted 📌 Requests coming from a single IP 📊 Logs Observed: Event ID 4625 (Failed Login) Repeated attempts within short time Same username pattern 🚨 Investigation Steps: 1️⃣ Checked Windows Security Logs 2️⃣ Identified repeated failures 3️⃣ Tracked source IP address 4️⃣ Correlated login patterns ⚠️ Indicators of Attack: 50+ failed attempts Same IP hitting continuously No successful login initially 👉 Conclusion: 🔥 Brute Force Attack Attempt Detected 🛠 Action Taken (SOC Response): ✔️ Blocked suspicious IP ✔️ Alerted security team ✔️ Recommended password reset ✔️ Enabled account lockout policy 🧠 Key Learning: 👉 Pattern + persistence = attack detection 💡 Why This Matters: Every SOC Analyst must: ✔️ Investigate logs ✔️ Identify attack patterns ✔️ Take quick action
0
0
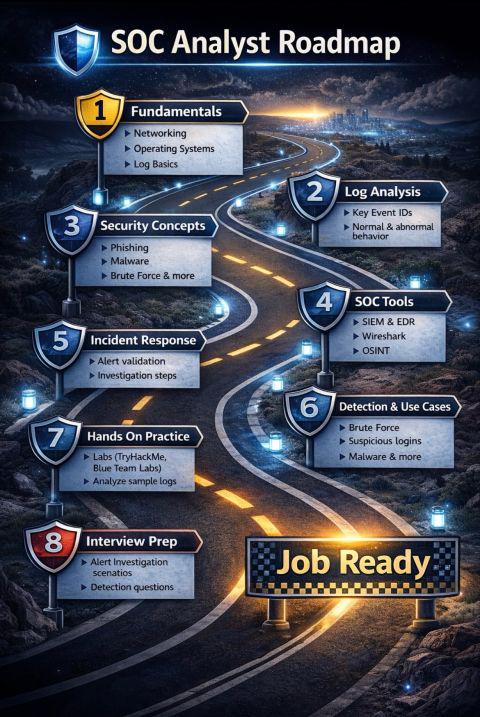
🛡️ SOC Analyst Roadmap (From Beginner to Job Ready)
Most people want to get into cybersecurity… But they get lost between courses, certifications, and random content. So here’s a clear, real world roadmap to become a SOC Analyst 👇 Btw I started a series based on this roadmap to help people who r new to this plz check my lastest posts to find notes and plan 🧱 1. Fundamentals Start with the basics: • Networking (TCP/IP, DNS, Ports, HTTP/HTTPS) • Operating Systems (Windows + Linux) • Understanding logs 👉 If you don’t understand how systems work, you won’t understand attacks. 🔍 2. Log Analysis This is the core skill of a SOC Analyst. Focus on: • Event ID 4624 → Successful logon • Event ID 4625 → Failed logon • Event ID 4688 → Process creation • Sysmon logs 👉 Learn to identify normal vs suspicious behavior 🧠 3. Security Concepts Understand how attacks actually happen: • Phishing • Malware • Brute force attacks • Privilege escalation • MITRE ATT&CK 👉 Stop memorizing. Start thinking like an attacker. 🛠️ 4. SOC Tools Get hands-on with tools used in real environments: • SIEM (Splunk / Sentinel) • EDR solutions • Wireshark (network analysis) • VirusTotal (file & URL analysis) • OSINT tools 👉 Tools don’t make you skilled. Knowing what to look for does. 🚨 5. Incident Response Every alert follows a process: 1. Alert triggered 2. Validation (True/False positive) 3. Investigation (User, IP, Process) 4. Containment 5. Reporting 👉 This is what you’ll actually do in a SOC job. 🔍 6. Detection & Use Cases Learn how to detect real attacks: • Brute force → Multiple failed logins • Suspicious login → Unusual time/location • Malware → Abnormal processes • Privilege escalation 👉 Anyone can see alerts. Few understand them. 🧪 7. Hands-On Practice This is where most people fail. • TryHackMe labs • Blue Team labs • Analyze real-world logs 👉 Practice is what makes you confident in interviews. 🎯 8. Interview Preparation Prepare to explain, not just answer: • SOC roles & responsibilities
0
0
1-10 of 20
@aladin-umar-9259
✨ Helping People Sell Digital Products on IG 💸 Turn Your Ideas into Cash | UGC 🚀 50k Followers in 120 days 👇 FREE👇 Money Guides 💸 ↓
Active 5h ago
Joined Apr 5, 2026

